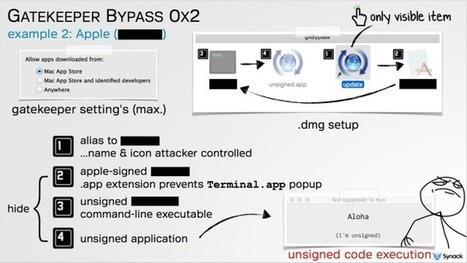
AppleInsider reports that a vulnerability first disclosed to Apple three months ago remains unpatched and now the security researcher who found it has gone public. Filippo Cavallarin has published details of how the vulnerability enables a user to be tricked into running malicious applications, bypassing the Gatekeeper function in the process.
Gatekeeper is the Apple mechanism that has, since 2012, been enforcing the code signing and verification of application downloads. If a user were to download an app outside of the Mac App Store then Gatekeeper would kick in and prevent it from running without the express consent of the user. In theory anyway.
Cavallarin says that, on macOS X version 10.14.5 (Mojave) and below, it is possible to "easily bypass Gatekeeper in order to execute untrusted code without any warning or user's explicit permission." According to Cavallarin, he contacted Apple February 22 and the vendor is aware of the issue. It was, he says, "supposed to be addressed, according to the vendor, on May 15, but Apple started dropping my emails." As a 90 day disclosure deadline, which he says Apple is aware of, has now passed, Cavallarin has made details of the vulnerability public.
Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Gatekeeper



 Your new post is loading...
Your new post is loading...













Mac malware developers have jumped on a recently disclosed macOS Gatekeeper vulnerability and are actively developing malware that abuses it.
The new malware has been named OSX/Linker and has been tied to the same group that operates the OSX/Surfbuyer adware, according to an investigation carried out by Joshua Long, Chief Security Analyst for Mac security software maker Intego.
Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Gatekeeper