 Your new post is loading...
 Your new post is loading...

|
Scooped by
Terheck
|
"La Journée Mondiale pour un Internet plus sûr « Agir pour un meilleur Internet » organisée par Insafe de la Commission européenne se déroulera le 9 février 2016. Cette année, l’accent est mis sur l’initiation au code informatique et la création de contenus numériques par les jeunes.
Chaque année le Safer Internet day, (SID) évènement mondial, donne le coup d’envoi de manifestations - ateliers, formations - destinées à promouvoir une utilisation plus sûre et plus responsable de l’Internet chez les jeunes - qui se dérouleront pendant tout le mois..."

|
Scooped by
Terheck
|
Librarians have long understood that to provide access to knowledge it is crucial to protect their patrons' privacy. Books can provide information that is deeply unpopular. As a result, local communities and governments sometimes try to ban the most objectionable ones. Librarians rightly see it as their duty to preserve access to books, especially banned ones. In the US this defense of expression is an integral part of our First Amendment rights.
"Social media and text messages have blurred the lines between students’ school lives and private lives. While most schools take clear steps to protect students at school, more schools are beginning to consider the need to set policies that apply to students’ activities outside of school."
Via EDTECH@UTRGV

|
Scooped by
Terheck
|
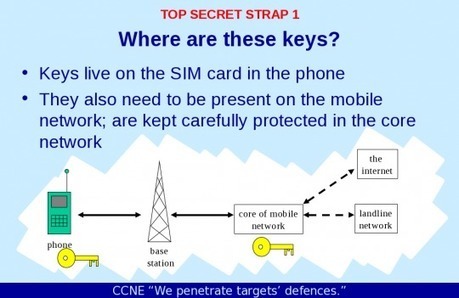
"AMERICAN AND BRITISH spies hacked into the internal computer network of the largest manufacturer of SIM cards in the world, stealing encryption keys used to protect the privacy of cellphone communications across the globe, according to top-secret documents provided to The Intercept by National Security Agency whistleblower Edward Snowden. The hack was perpetrated by a joint unit consisting of operatives from the NSA and its British counterpart Government Communications Headquarters, or GCHQ. The breach, detailed in a secret 2010 GCHQ document, gave the surveillance agencies the potential to secretly monitor a large portion of the world’s cellular communications, including both voice and data. The company targeted by the intelligence agencies, Gemalto, is a multinational firm incorporated in the Netherlands that makes the chips used in mobile phones and next-generation credit cards. (...)"

|
Scooped by
Terheck
|
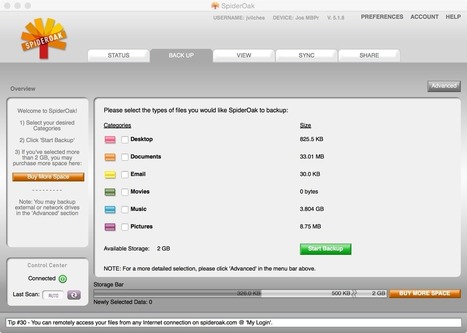
Users are increasingly turning to services that claim to be secure from the prying eyes of the NSA and law enforcement. In this article, we take a look at some of the privacy-focused email and cloud storage services that have either sprung up or gained popularity in the wake of what's popularly been referred to as the Summer of Snowden. Secure Email and Cloud Alternatives to Gmail and Dropbox.

|
Scooped by
Terheck
|
Laura Poitras’ riveting new documentary about mass surveillance gives an intimate look into the motivations that guided Edward Snowden, who sacrificed his career and risked his freedom to expose mass surveillance by the NSA. CITIZENFOUR, which debuts on Friday, has many scenes that explore the depths of government surveillance gone awry and the high-tension unfolding of Snowden’s rendezvous with journalists in Hong Kong.

|
Scooped by
Terheck
|
It's a fascinating, hour-long session in which Snowden articulates the case for blowing the whistle, the structural problems that created mass surveillance, and why it's not sufficient to stop the state from using our data -- we should also limit their ability to collect it. The Slashdot post by The Real Hocus Locus provides good timecode-based links into different parts of the talk.

|
Scooped by
Terheck
|
A security research reported the bug in iCloud's security to Apple back in March.

|
Scooped by
Terheck
|
Dan Geer's Black Hat 2014 talk Cybersecurity as Realpolitik (also available as text) is thoughtful, smart, vital, and cuts through -- then ties together -- strands of security, liability, governance, privacy, and fairness, and is a veritable manifesto for a better world.

|
Scooped by
Terheck
|
"Freedom of speech online could get a big boost The anonymous Internet is small. Too small, if you ask many activists, and it may need to grow 10, or even 50, times its current size, if its going to continue to support free speech around an increasingly digital world. Tor, the largest anonymizing network ever built, fundamentally relies on just 2,000 volunteer routers to relay 99 percent of its encrypted data around the globe (...)"

|
Scooped by
Terheck
|
EFF has released its first version of Privacy Badger, a new open source browser add-on for Firefox and Chrome that stops advertisers and other third-party trackers from secretly tracking where you go and what pages you look at on the web.

|
Scooped by
Terheck
|
Security bugs like Heartbleed make it abundantly clear that your logins and passwords are not safe. But what if you could use the Web for common tasks like uploading photos and videos or chatting with friends, all without signing up for an account? Guarding your privacy is important. There are obvious benefits to having logged…

|
Scooped by
Terheck
|
"You are being watched on the Internet – but if you use Mozilla Firefox, some of its great add-ons can help protect your privacy and security on the Web. Now, be warned that none of these are going to be completely foolproof. In fact, there's is no completely safe way to use the Internet. But for most regular users, the protection that these extensions and tools offer will be enough as safeguards..."
|

|
Scooped by
Terheck
|
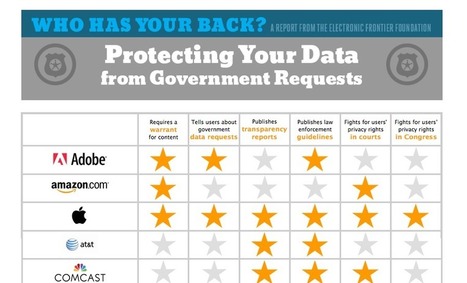
EFF has released its newest report charting which companies promise to uphold best practices in privacy and transparency. The report analyzes the published policies of 24 major technology companies, including Facebook, Google, Twitter, and ISPs like AT&T and Comcast. While we've released this report for four years, this year we made the criteria more challenging to reflect the higher standards we've come to expect from technology companies.
In this year's Who Has Your Back, nine companies earned stars in every category available to them: Adobe, Apple, CREDO, Dropbox, Sonic, Wickr, Wikimedia, Wordpress.com, and Yahoo. Three companies scored especially poorly: AT&T, Verizon, and WhatsApp.

|
Scooped by
Terheck
|
"The House of Representatives passed bipartisan legislation on Wednesday designed to help companies and the federal government better defend against the growing threat of cyberattacks, despite opposition from privacy advocates. Passed by a 307-116 vote, the controversial Protecting Cyber Networks Act encourages US companies to share information about security breaches with the federal government by providing them with expanded legal liability protections. Prompted in part by a recent uptick in high-profile data breaches, the legislation would allow companies to share information through a "cyber portal" administered by the Department of Homeland Security..."

|
Scooped by
Terheck
|
The boom in smartphones among often careless users has made happy hunting for hackers, whose virus attacks and hijacking of unprotected mobiles are multiplying, experts warn.

|
Scooped by
Terheck
|
"Internet surveillance has been a hot topic in recent years—we’ve talked about it extensively here at MakeUseOf, it’s been brought up on major news outlets daily, and we’ve seen a slew of new apps, extensions, and products aimed at helping you retain your privacy online. This article is meant to be as comprehensive a resource as possible on avoiding Internet surveillance. We’ll talk about why Internet surveillance is such a big deal, who’s behind it, whether or not you can completely avoid it, and a wide range of tools that will make you harder to track, identify, and spy on..."

|
Scooped by
Terheck
|
"The problem with encrypting data is that sooner or later, you have to decrypt it. Keep your cloud files cryptographically scrambled using a secret key that only you possess, and it’s likely no hacker will have the codebreaking resources necessary to crack them. But as soon as you want to actually do something with those files—anything from editing a word document or querying a database of financial data—you have to unlock the data and leave it vulnerable. Homomorphic encryption, a still-mostly-theoretical advancement in the science of keeping secrets, could change that (...)"

|
Scooped by
Terheck
|
Tips, Tools and How-tos for Safer Online Communications EFF announce the relaunch of Surveillance Self-Defense, their guide to defending yourself and your friends from digital surveillance by using encryption tools and developing appropriate privacy and security practices. These resources are intended to inspire better-informed conversations and decision-making about digital security and privacy. The site is available today in English, Arabic, and Spanish, with more languages coming soon.

|
Scooped by
Terheck
|
According to Edward Snowden, people who care about their privacy should stay away from popular consumer Internet services like Dropbox, Facebook, and Google...
Il y a quatre ans, un collectif s'est attaché à rédiger un guide d'autodéfense numérique afin de permettre à chacun d'utiliser les technologies numériques en ayant connaissance des bonnes pratiques en la matière. S'il ne prétend pas donner accès à une protection parfaite, ce guide offre toutefois des pistes pour appréhender correctement les outils technologiques et réduire la surveillance électronique.
Via Frédéric DEBAILLEUL

|
Scooped by
Terheck
|
With 500 attendees and some big names from the data privacy and human rights fields, the Don't Spy on Us Day of Action was a fascinating afternoon of discussion, debate, and practical advice on how to keep our personal data private from snooping governments. I learned a lot, and I've condensed the most important parts…

|
Scooped by
Terheck
|
"When governments are after your personal data, which online services will stand up and defend it? In our fourth annual Who Has Your Back report, we look at companies' public policies and practices, so that privacy-conscious consumers can make an informed decision about who to trust with their most sensitive data..."

|
Scooped by
Terheck
|
We live within our web browsers. You're reading this article in a web browser. You probably check your email in a web browser. I order my groceries in a web browser. I buy books in a web browser. Web browsers are pretty important. But we never really think about them within the context of security…

|
Scooped by
Terheck
|
The ACLU hopes to facilitate the debate by making these documents more easily accessible and understandable. This tool will be an up-to-date, complete collection of previously secret NSA documents made public since last June. The database is designed to be easily searchable – by title, category, or content – so that the public, researchers, and journalists can readily home in on the information they are looking for.
|
 Your new post is loading...
Your new post is loading...
 Your new post is loading...
Your new post is loading...






























Pour préparer le Safer Internet Day, le site docpourdocs propose de nombreux liens vers d'intéressantes ressources.
A regarder pour préparer quelques séances à cette occasion.